Mastering Risk: A Hacker’s Playbook
Risk isn’t something to fear—it’s something to master. Learn how to think critically, uncover vulnerabilities, and turn threats into opportunities.

Imagine this: You’re a hacker analyzing a target. Every vulnerability is an entry point, every threat a puzzle to solve. Now, flip the script—what if your mission was to defend instead of attack? Same mindset, different goal.
Risk assessments aren't about checking a box; they're about thinking critically, anticipating threats, and hacking risks before they hack you. Whether you're securing an organization or leveling up your GRC skills, this guide will show you how—even if you're not in the job yet.
Rewire How You Think About Risk
Where others see roadblocks, hackers see opportunities. Hackers break threats apart and find solutions—a mindset that's pure gold in risk assessments.
Don't dodge risks; treat them as puzzles to solve and challenges to control. It's not about fear; it's about curiosity and growth. It's an opportunity to learn, adapt, and fortify your defenses.
Think like an attacker, act like a defender. Hack the process. Own the results.
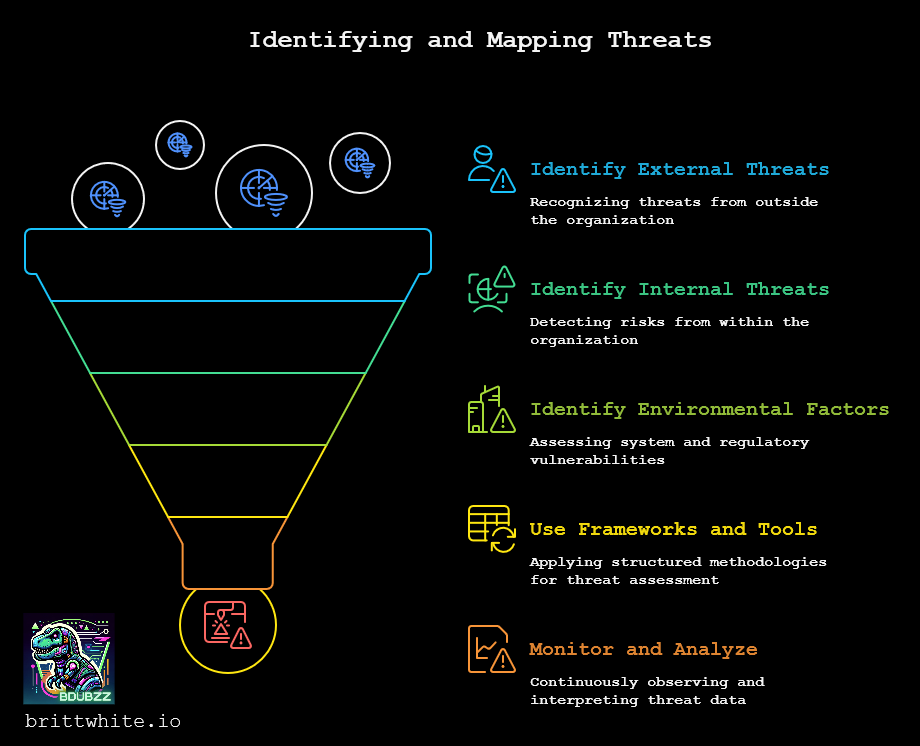
Mapping the Threat Landscape
Every hacker starts with recon—gathering intel to understand their target. In a risk assessment, the target is your organization’s threat landscape, which includes:
- External threats: Cyber criminals, natural disasters, or supply chain nightmares
- Internal threats: Insider misuse, misconfigurations, or Carl in accounting clicking phishing emails
- Environmental factors: Outdated systems, evolving regulations, or that dusty server still running Windows XP
To identify these threats, lean on tools and frameworks like MITRE ATT&CK, STRIDE, or NIST CSF 2.0, paired with actionable steps:
→ Monitor threat intelligence feeds
→ Dig into recent breach reports for your industry
→ Ask, "What could go terribly wrong here?"
Threats exist everywhere—but they only become risks when vulnerabilities open the door. The key to defense? Spot those weak points before attackers do.
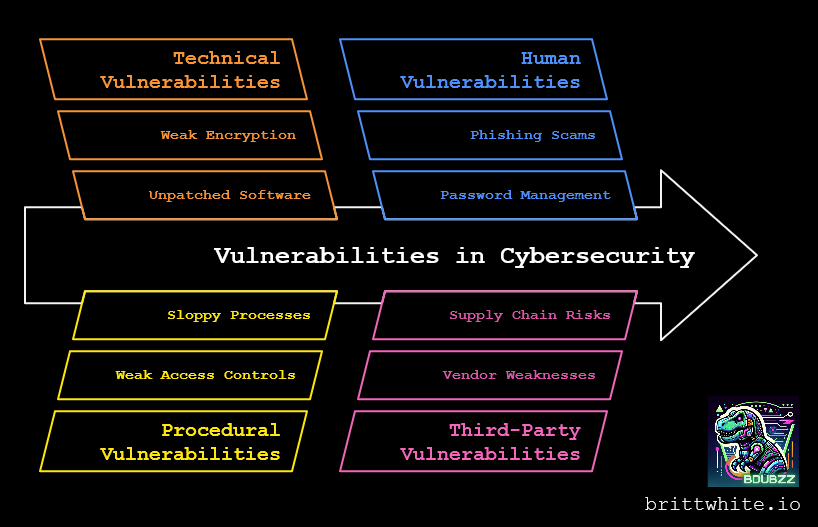
Find Weaknesses Before Hackers Do
For hackers, vulnerabilities are like backdoors left unlocked—quiet, easy, and waiting to be exploited. Risk assessments help you find and bolt them shut before attackers slip through.
Vulnerabilities come in three categories:
- Technical: Unpatched software, weak encryption, or the server from 2005 still running in the back closet
- Procedural: Weak access controls, sloppy processes, or workflows held together with duct tape
- Human: Falling for phishing scams, shadow IT, or passwords written on sticky notes
Use tools like vulnerability scanners (e.g., Nessus) and frameworks like CVSS and OWASP Top Ten to identify and assess weaknesses. But don't stop there—talk to your team. Those on the front lines often know where the real cracks are hiding. And always vet third-party relationships, known as due diligence, because hackers don't care if the weak link is inside your network or your vendor's.
The trick? Think like an attacker. If you wanted in, where would you strike first?
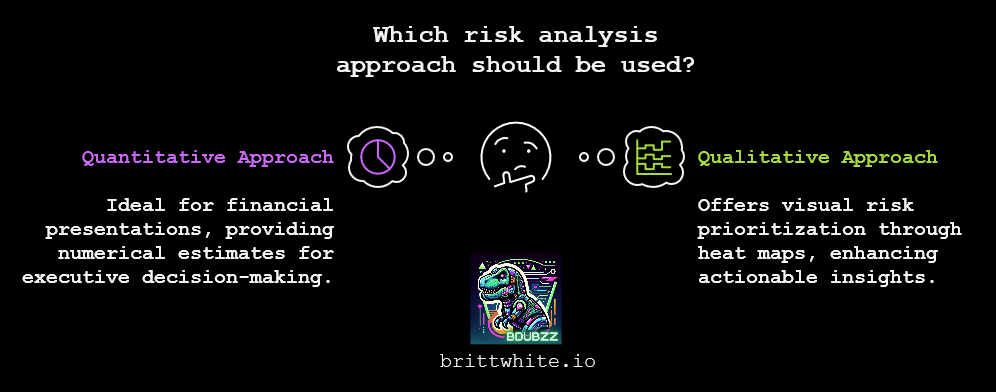
The Secret Sauce
Risk = Threat × Vulnerability × Impact
This formula is the foundation of every risk assessment—it helps separate real threats from the background noise.
When analyzing risks, choose your approach:
- Quantitative: Assign numerical values (e.g., financial loss estimates); ideal for presenting to executives like the Chief Financial Officer (CFO)
- Qualitative: Use heat maps to visualize risks and prioritize actions; great for clear and actionable insights
Building a risk profile is like creating a hacker's "attack map" in reverse. Instead of planning infiltration, you're identifying where and how to defend.
By shifting from reactive to proactive defense, you're not just managing risks—you're controlling the narrative.
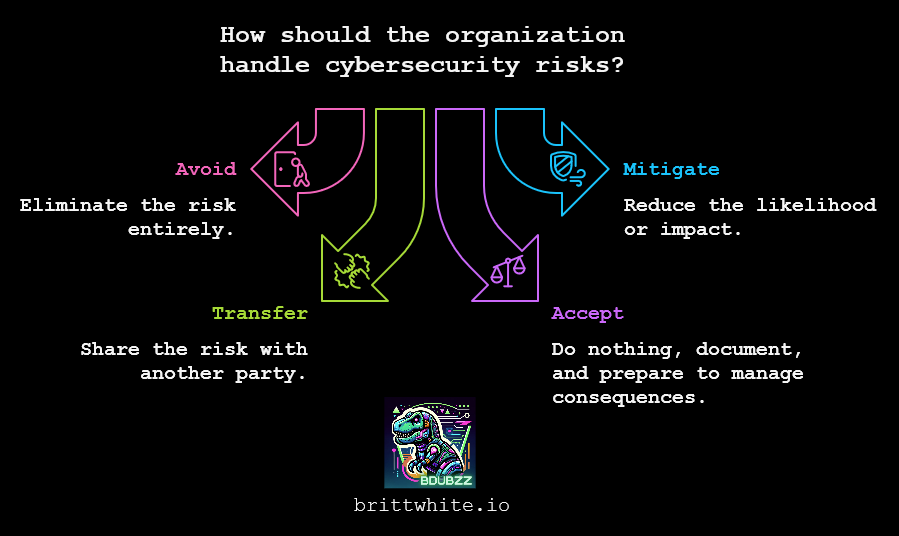
Your Risk Defense Game Plan
Hackers don’t just find vulnerabilities—they exploit them. Your job? Neutralize them before they strike. Here’s how:
- Avoid: Eliminate the risk entirely (e.g., decommission outdated systems)
- Mitigate: Reduce the likelihood or impact (e.g., enforce MFA, patch systems, tighten access controls)
- Transfer: Share the risk (e.g., invest in cyber insurance or outsource to a third-party)
- Accept: If mitigation costs exceed the risk, document the decision and prepare to manage the consequences
Mitigation is just the first move—staying ahead is the real game. Risk isn't static; threat evolve, vulnerabilities emerge, and security requires constant vigilance.
Build Your GRC Skills Today
Want to break into GRC? Stop waiting—start hacking your experience. You don't need a job title to start thinking like a risk pro.
Here’s your game plan:
- Pick a scenario: Choose a small business, nonprofit, or your favorite local coffee shop
- Research threats: Identify external risks (cyberattacks, natural disasters) and internal risks (misconfigurations or Carl in accounting)
- Map vulnerabilities: Note weaknesses like unpatched software or human error
- Analyze risks: Use the formula
Risk = Threat × Vulnerability × Impactto prioritize - Recommend mitigations: Propose practical solutions and document them in a professional report
This hands-on approach builds skills and creates proof. A portfolio of mock assessments demonstrates initiative, creativity, and problem-solving—exactly what employers want.
Need help getting started? Check out my blog, GRC Skills: Create Your Opportunity, for actionable steps to gain GRC experience and break into the field.
Master Risks, Secure Your Future
Bottom line? Risk isn't something to fear—it's something to master. Choose a scenario, start assessing risks, and hack your way to confidence.
Your next move? Start assessing, defend like a pro, and level up your skills. Security isn't just about avoiding threats—it's about anticipating them.
